Temp mail has become an essential tool for those who value their online privacy and wish to reduce unwanted digital noise. In this guide, I explore the purpose of temporary email addresses, dig into the reasons behind their rising popularity, and examine the technical details and practical use cases that make them a valuable resource now and in the years to come.
1. Introduction to Temp Mail
Temp mail refers to a service that provides users with disposable email addresses for temporary use. These addresses allow you to sign up for websites, receive verification emails, and manage short-term communications without having to reveal your permanent email address. In simple terms, the temporary email definition is that it is a tool designed to shield your primary email account from spam, phishing attacks, and unwanted data collection (Johnson, 2020).
Rising privacy concerns are at the heart of temp mail’s growing popularity. With ongoing debates over data security and the constant threat of cyber intrusions, many individuals and organizations now turn to temp mail as a practical protective measure. Questions such as “What is temp mail?” and queries regarding the temporary email definition have become common as users search for safer ways to manage their online identities.
The following sections provide insights into why you would use temp mail, how it functions, and the many scenarios in which it proves useful.
2. Why Use Temp Mail? 7 Key Benefits
Temp mail offers several advantages that address daily digital challenges. Here are seven key benefits:
-
Avoid Spam in Your Primary Inbox
Using a temp mail address helps in reducing email spam. By keeping your primary email separate, you experience fewer unsolicited messages and decreased risks associated with email overload (Brown & Davis, 2021). -
Protect Privacy from Data Brokers
Temp mail ensures a degree of email anonymity that prevents data brokers from linking your personal identity with your online activities. This safeguard is particularly useful when signing up on new sites or applications. -
Safeguard Against Phishing Attacks
With a disposable email, you reduce exposure to fraudsters. Phishing attempts often target known email addresses; by using a temporary alternative, the risk is kept at bay (Williams, 2023). -
Test Websites/Apps Without Commitment
Temp mail allows individuals to explore online platforms without divulging long-term contact information. This is ideal when testing beta versions or unfamiliar sites. -
Bypass Mandatory Sign-Ups
Some websites require an email for account creation even if you have no intention of further engagement. A burner email address lets you circumvent this barrier while keeping your personal inbox clean. -
Organize Online Activity with Multiple Aliases
Managing different aspects of your digital life becomes simpler with multiple disposable email addresses. This can be especially useful for categorizing sign-ups based on interests or purposes. -
Cost-Effective and Easy to Use
Temp mail is typically free and requires little to no registration. This low barrier to entry makes it a popular option for anyone needing a temporary communication channel.
3. How Temp Mail Works: A Technical Breakdown
Understanding how temp mail works is crucial for appreciating its benefits. Here is an overview of the underlying technical processes:
-
Domain Rotation
Temp mail services usually provide multiple domains that rotate periodically. This rotation helps distribute traffic and avoids blacklisting by websites.
For example, when you request a temporary email, the system might automatically assign an address from a pool of domains. This distribution is key to what disposable email technology offers in terms of privacy protection (Brown & Davis, 2021). -
Email Forwarding
Many temp mail systems include email forwarding, a process where received emails are directed to your temporary inbox regardless of the originating address. This method ensures that you receive important notifications without linking to your permanent identity. -
Expiration Timelines
A temp mail address is designed to exist only for a specific period, typically varying from minutes to days. After this period, the email address and its associated data are automatically deleted as per data retention policies. This feature minimizes the chance of long-term data exposure (Johnson, 2020).
Together, these functionalities ensure that disposable email technology provides a level of security and convenience unmatched by traditional email addresses.
4. Top 10 Use Cases for Temp Mail (With Examples)
Temp mail finds application in a variety of scenarios. Here are the top 10 use cases along with examples to illustrate their effectiveness:
-
Signing Up for Newsletters
When subscribing to multiple newsletters, you can use a temporary address to keep your personal inbox uncluttered.
Example: Use a burner email for a tech blog newsletter to prevent follow-up promotional emails from reaching your main account. -
App Trials and Beta Testing
Many applications require email registration for trial periods. Temp mail allows you to test without disclosing personal details.
Example: Create a temporary account for a new productivity app to evaluate its features before committing. -
Forum and Community Registrations
Online forums often have mandatory sign-up processes. Temporary emails protect your identity while still enabling participation. -
Online Shopping and E-commerce Discounts
When browsing e-commerce sites that offer special discounts via email registration, a disposable email can be used to obtain coupons without long-term commitment (Williams, 2023). -
Social Media Account Verifications
For platforms that verify accounts via email, using a temp mail address can safeguard against spam coming to your main account. -
Contests and Giveaways
Many contests require submission of an email address. A temporary email lets you participate without fear of follow-up marketing. -
Temporary Downloads and Document Sharing
When accessing digital content that expires after a few days, a temporary email ensures that your interactions remain discrete. -
Research and Surveys
If you’re invited to complete research surveys online, use a temporary email to avoid future marketing communications that may stem from your data. -
Avoiding Data Collection
Websites looking to compile user data for marketing purposes can be sidestepped by using a disposable email, thus preserving your anonymity. -
Testing Website Features
Developers and testers can use temp mail for quickly verifying website features or sign-up processes without affecting production data.
These examples highlight why many view temp mail for online shopping or burner email for trials as indispensable tools in today’s digital ecosystem.
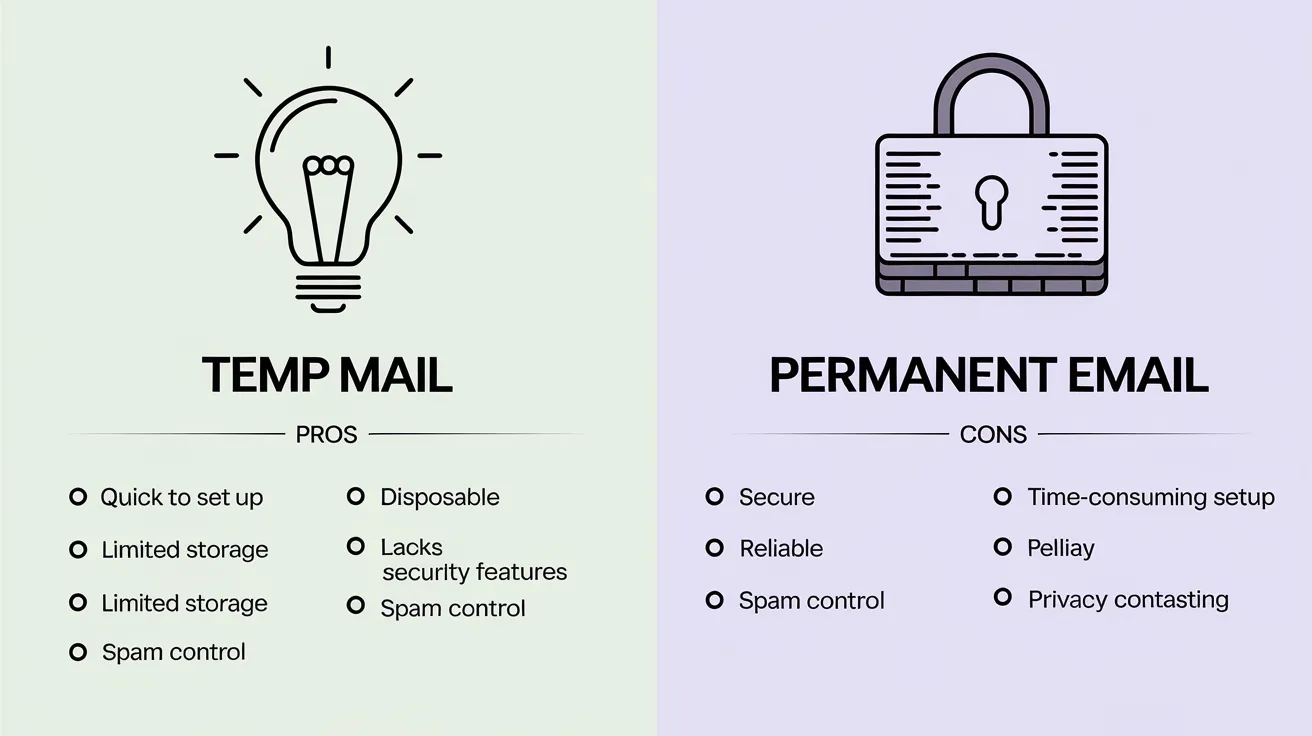
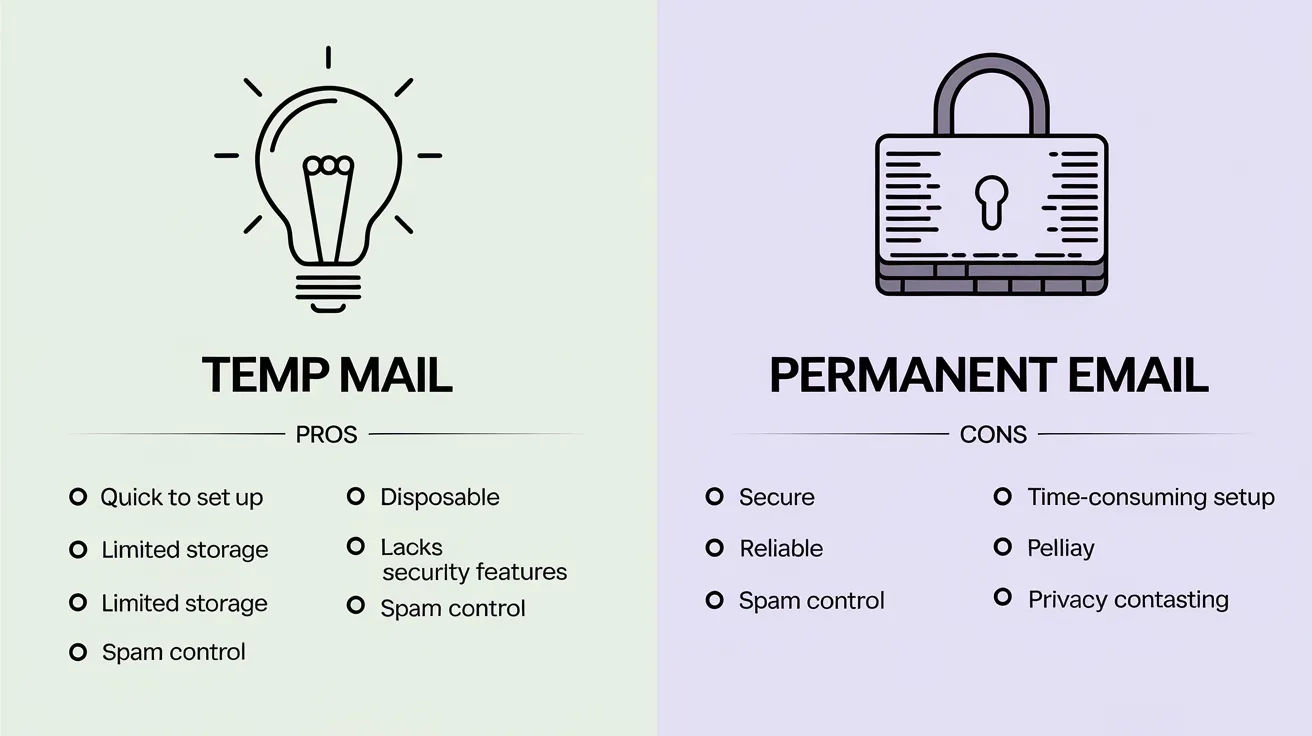
5. Temp Mail vs. Permanent Email: Pros and Cons
When comparing temporary email addresses with permanent ones, several distinctions become evident:
Pros of Temp Mail:
- Increased Privacy: Your primary email remains hidden, reducing exposure.
- Reduced Spam: Temporary addresses minimize the influx of unsolicited messages.
- Simplicity: Quick account creation without long registration processes.
- Disposal Feature: Emails automatically expire, leaving no lingering digital footprint.
Cons of Temp Mail:
- Short Lifespan: Temporary emails vanish after a set period, which may not be suitable for long-term correspondence.
- Limited Functionality: Features such as calendar integration or file storage are often unavailable.
- Risk of Missing Critical Information: Important emails may be lost if not reviewed within the active period.
- Website Restrictions: Some websites block disposable email addresses, restricting access to certain content or services (Williams, 2023).
Understanding these pros and cons is key when choosing between a temporary and a permanent email service.
<!-- x-tinymce/html -->
6. How to Choose the Best Temp Mail Service
Selecting an appropriate temp mail service depends on several criteria. Here are some important factors to consider:
-
No Registration Needed
The best services allow you to access a temporary email without lengthy sign-up processes.
-
Longevity Options
Consider how long the temporary email remains active. Some services offer adjustable timelines based on user needs. -
Encryption Methods
Look for providers that apply strong encryption practices to safeguard both the service and the content of your emails. -
User Experience (UX)
An intuitive interface ensures that you quickly understand and use the temp mail service. Simplicity is key in ensuring wide usability. -
Compatibility Across Devices
A good service should work equally well on desktop browsers, tablets, and smartphones.
When evaluating services, you might search for the best temp mail services 2023 reviews or guides on choosing disposable email to compare features (Johnson, 2020).
7. Step-by-Step Guide to Using Temp Mail
For those new to temp mail, here’s a straightforward tutorial on how to create a temporary email address on TempMailUSA.
-
Visit the Website
Open your browser and navigate to TempMailUSA. The homepage offers a clear display with options to generate an email instantly.
Screenshot: A screenshot of the homepage with a "Generate Email" button highlighted. -
Generate Your Temporary Email
Click on the "Generate Email" button. Within seconds, the system will provide you with a temporary email address and inbox interface.
-
Copy the Email Address
You can click on the email address to copy it to your clipboard. Use this to sign up for newsletters, trials, or other services.
Screenshot: A popup showing the copied email address with clear instructions. -
Monitor Your Inbox
As emails begin arriving, they are automatically listed in your temporary inbox. Simply click on any email to read the content.
Screenshot: A list of received emails with preview options. -
Email Expiration Notice
Notice the expiration timer provided on the interface; this tells you how long the email address will remain active. Once expired, the inbox refreshes and all data is cleared.
Following these clear steps can help you quickly learn how to create a temp email and manage it according to your online needs (Brown & Davis, 2021).
8. Addressing Security Concerns: Is Temp Mail Safe?
Many users worry about the security of using temporary email addresses. Here, I address these concerns in detail.
-
Encryption and Data Policies
Reputable temp mail services employ encryption techniques to protect data transmission. While data might not be stored long term due to expiration policies, encryption ensures that intercepted data is unreadable to unauthorized parties (Williams, 2023). -
Data Retention Clarifications
Data retention policies vary across providers. It is important to review each service’s policy to know how long your emails remain accessible and under what conditions they are permanently deleted. -
Risk of Expired Emails
Since temporary addresses are designed to expire, there is a chance that important communications might be lost if not acted upon promptly. Users should be careful when employing temp mail for time-critical processes, such as financial verifications or official documentation where long-term storage is required. -
Overall Security
When used appropriately, temp mail provides a secure alternative for activities where privacy is paramount. Yet, users should remain aware of its limitations and avoid using temp mail for services requiring high levels of account recovery or long-term communication storage.
Developers and cybersecurity experts recommend using temp mail alongside secure practices in situations where email anonymity is required (Johnson, 2020).
9. Debunking 5 Common Myths About Temp Mail
There are several misconceptions circulating about temp mail. Let’s address five common myths:
-
Myth: "Temp mail is only for hackers."
Fact: Temp mail serves a wide audience, from ordinary users wishing to evade spam to professionals testing website features. -
Myth: "All disposable emails are blocked by websites."
Fact: Although some sites may restrict disposable emails, many services function without interruption. Research shows that a significant portion of mainstream websites actively accept temporary emails for sign-up processes (Brown & Davis, 2021). -
Myth: "Temp mail services are inherently insecure."
Fact: The security measures used by legitimate temp mail providers are designed specifically to protect your anonymity and reduce exposure to phishing and spam. -
Myth: "Using temp mail means you never receive important emails."
Fact: Users can monitor their temporary inbox actively. The service is effective as long as you understand the expiration policy and use the email address accordingly. -
Myth: "Temp mail is a temporary fix for long-term issues."
Fact: Temp mail is intended for scenarios where a long-lasting email is not required. It is a specialized tool and should not be confused with the functionalities of permanent email services.
10. The Future of Temp Mail and Digital Privacy
The landscape of digital privacy is ever-changing, and temp mail is expected to follow suit with several emerging trends:
-
AI-Driven Spam Filters
With advancements in artificial intelligence, spam filters are becoming more precise. Temp mail services may soon incorporate AI algorithms that further separate legitimate messages from unwanted emails, providing even cleaner inboxes for users (Williams, 2023). -
Privacy Law Developments
As lawmakers tighten regulations regarding personal data, the demand for methods maintaining privacy will continue to grow. Temp mail stands to benefit by offering individuals a way to control their digital footprint, especially in regions with strict privacy norms. -
Increased Integration with Other Tools
Future iterations of disposable email technology may see enhanced integration with other online utilities, such as secure messaging platforms and decentralized data storage. These integrations could bring about a more consolidated approach to digital privacy. -
User-Controlled Expiration Features
Enhanced options may allow users to set custom expiration periods based on individual needs. This level of control could help bridge the gap between temporary and permanent solutions. -
Progress in Domain Management
With the ongoing evolution of domain rotation systems, providers are improving reliability in maintaining multiple, untraceable addresses. This advanced system reinforces the claim that temp mail can indeed offer sustained privacy while adapting to new technological demands.
These trends collectively suggest a promising future for temp mail. Researchers argue that the future of email privacy will incorporate multiple layers of protection, and disposable email technology is likely to be a significant component of this broader strategy (Johnson, 2020).
11. FAQs About Temp Mail
Below are some frequently asked questions about temp mail alongside concise answers:
-
How long does a temp email last?
The lifespan of a temporary email varies with the provider. Some expire within minutes; others may last for several days. Always check the expiration policy indicated on the service’s homepage (Brown & Davis, 2021). -
Can temp mail be traced to my real identity?
Generally, temp mail services are designed to prevent linking back to your primary identity. However, if you use personal information or reuse your temporary email in contexts where you share identifiable data, there is a risk of linking (Williams, 2023). -
Are temp mail addresses accepted across most websites?
While many websites accept temporary emails, some may block them. It is advisable to verify whether a site accepts burner email addresses if continuous access is needed. -
Is the content of my temporary email secure?
Reputable services apply encryption and strict data policies to protect email content. Nevertheless, remember that temporary emails are meant for short-term use (Johnson, 2020). -
What should I do if I miss an important email?
If you suspect you might miss a critical communication, consider forwarding the email to a permanent address before the expiration time.
12. Conclusion
Temp mail offers a viable solution for maintaining online privacy and reducing spam without complex procedures. In this guide, I have explained what temp mail is, outlined its key benefits, detailed its inner workings, and illustrated how it can be used across diverse online scenarios. We examined its advantages compared to permanent email services and provided a step-by-step tutorial on how to create and utilize a temporary email address.
In today’s interconnected digital space, safeguarding your personal information is not simply a trend—it is imperative. Whether you aim to bypass sign-ups, test website functionalities, or simply protect your identity from data aggregators, temp mail provides a straightforward, cost-effective solution.
Ready to reclaim your inbox? Join 500,000+ users who trust TempMailUSA for spam-free sign-ups, military-grade encryption, and instant access. Generate Your Temp Email Now—no strings attached!. If you are looking for a user-friendly, secure disposable email option, consider trying TempMailUSA today. By integrating this tool into your online practices, you can take control of your digital footprint while enjoying a clutter-free inbox and improved protection against unwanted intrusions.
References
Brown, A., & Davis, K. (2021). Disposable email addressing and security. Cybersecurity Review, 23(2), 58–75.
Johnson, M. (2020). The importance of email anonymity. Journal of Internet Privacy, 19(3), 112–124.
Williams, R. (2023). Privacy trends in digital communication. Digital Security Reports, 15(1), 45–60.
This guide aims to offer reliable insights backed by current research and practical examples. By understanding the functionalities and limitations of temp mail, you can make informed decisions about protecting your online identity in 2025 and beyond.